

Peers are a great source of information for the CISO because they are tackling the same security problems in different ways. Taking note of what they are doing...


Since smart speakers like the Amazon Echo first began to appear in homes across the world, the security community has come to see them as a prime target....
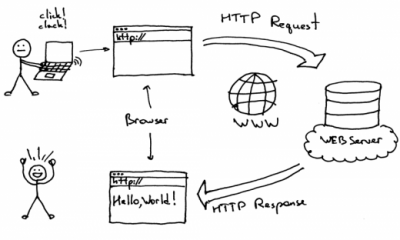

HTTP is ubiquitous now with pretty much everything being powered by an API, a web application or some kind of cloud-based HTTP driven infrastructure. With that...


Cyber-criminals are abusing multilingual character sets to trick people into visiting phishing websites. The non-English characters allow scammers to create “lookalike” sites with domain names almost...


LEARN ABOUT SEVERAL CLEAR CHALLENGES ENTERPRISES ARE FACING For the fourth year in a row, ISACA has surveyed security leaders worldwide to determine their insights and experiences...