According to the report, which was first delivered to The New York Times and is slated to become widely available Monday, the hacker group, which includes members from Russia, China and Europe, has been active since late 2013, stealing from more than 100 banks in 30 countries.
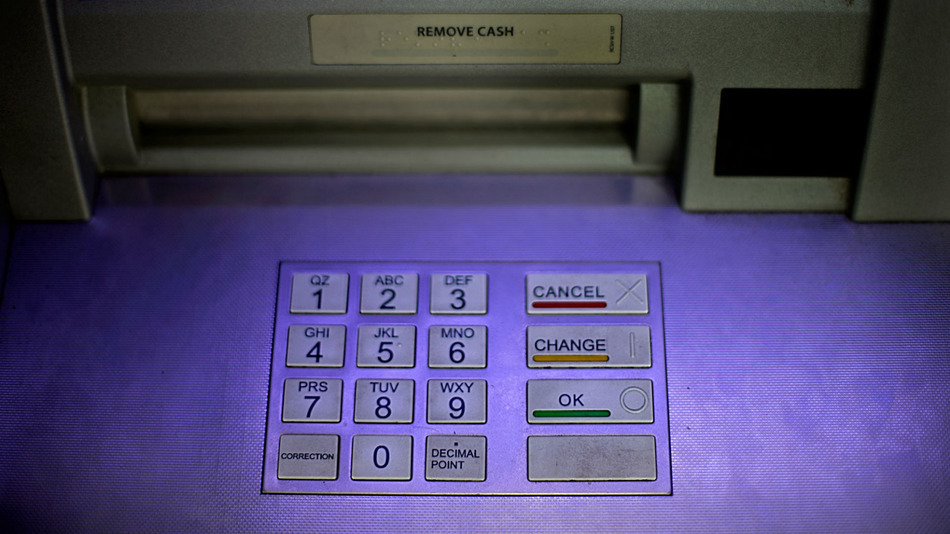
To do this, hackers used malware that infiltrated the banks’ computers, looking for weaknesses in their daily operations. After months of surveillance, hackers used an old tactic: impersonating bank officers, using false credentials to transfer millions of dollars to their accounts. The hackers also programmed ATMs to dispense money at specific times.
The hackers seemed to limit their theft to about $10 million before moving on to another bank, part of the reason why the fraud was not detected earlier, Kaspersky principal security researcher Vicente Diaz said in a telephone interview with The Associated Press.
The attacks are unusual because they target the banks themselves rather than customers and their account information, Diaz said. The goal seems to be financial gain rather than espionage, he said.
“In this case they are not interested in information. They’re only interested in the money,”
“In this case they are not interested in information. They’re only interested in the money,” he said. “They’re flexible and quite aggressive and use any tool they find useful for doing whatever they want to do.”Most of the targets have been in Russia, the U.S., Germany, China and Ukraine, although the attackers may be expanding throughout Asia, the Middle East, Africa and Europe, Kaspersky says.
Kaspersky did not identify the banks and is still working with law-enforcement agencies to investigate the attacks, which the company says are ongoing, and no bank has publicly acknowledged the theft yet. So far, Kaspersky has seen evidence of $300 million stolen, but the company believes the total amount is at least thrice as big.
The Financial Services Information Sharing and Analysis Center, a nonprofit that alerts banks about hacking activity, said in a statement that its members received a briefing about the report in January.
“We cannot comment on individual actions our members have taken, but on balance we believe our members are taking appropriate actions to prevent and detect these kinds of attacks and minimize any effects on their customers,” the organization said in a statement. “The report that Russian banks were the primary victims of these attacks may be a significant change in targeting strategy by Russian-speaking cybercriminals.”
The White House is putting an increasing focus on cybersecurity in the wake of numerous data breaches of companies ranging from mass retailers like Target and Home Depot to Sony Pictures Entertainment and health insurer Anthem.
The administration wants Congress to replace the existing patchwork of state laws with a national standard giving companies 30 days to notify consumers if their personal information has been compromised.
source:http://mashable.com/2015/02/16/hackers-steal-1-billion-from-banks/