Security
Internal Google Memo Responds To EU Antitrust Objections


Following reports about the European Union preparing to file formal charges against Google in its ongoing antitrust investigation, Google General Counsel Kent Walker has issued an internal memo to all employees. TechCrunch obtained the memo and it is reproduced in its entirety below.
In the letter, the counsel also notes that the EU is likely to open an investigation into its mobile operating system, Android, as well.
In the document, Google presents the case that there is a robust amount of competition in the areas that the commission is concerned with. It includes a variety of charts and graphs to support its rebuttals.
“An [Statement of Objections] is not a final finding. It’s a document in which the Commission staff sets out its preliminary arguments so that the company in question can respond,” says Walker. “Expect some of the criticism to be tough. But remember, it’s also an opportunity for Google to tell our side of the story.
“We have a very strong case, with especially good arguments when it comes to better services for users and increased competition,” Walker continues. And he says that Google has a ‘very strong case’ on Android, as well.
News Corp., publisher of the Wall Street Journal, filed a formal complaint with the EU Commission in regards to Google’s business practices this week. After a WSJ piece painted a picture of Google as wielding “undue political influence,” Google responded with a GIF-laden blog post detailing the interactions of its staff with Washington.
The Wall Street Journal and the Financial Times were among the first to report this week that the EU would bring antitrust charges against Google. EU antitrust head Margrethe Vestager and European Commission President Jean-Claude Juncker made a decision on filing charges on Tuesday, according to a WSJ source.
Google has faced antitrust investigation from the US Federal Trade Commission in the past, which found that Google did not violate American antitrust law. A european investigation into the competitive nature of its search services began in 2010, and it settled a case with European competition regulators in early 2014.
Last month, the WSJ published every other page of a 2012 FTC report that was sent to the publication accidentally, detailing its antitrust investigations. The report noted that the FTC found that it was a ‘close call’ whether Google violated antitrust regulations with its search product — but that it decided it had not. The document indicated that at least some inside the FTC felt that Google had acted in an anticompetitive manner.
Google declined to comment on the contents of the memo.
Google Argument
In the memo, Google argues that its search products have strong traditional competition, as well as new forms of competition. Google name-checks the usual search suspects including Bing and Yahoo, but also cites new services like Siri and Cortana that contain search-like capabilities.
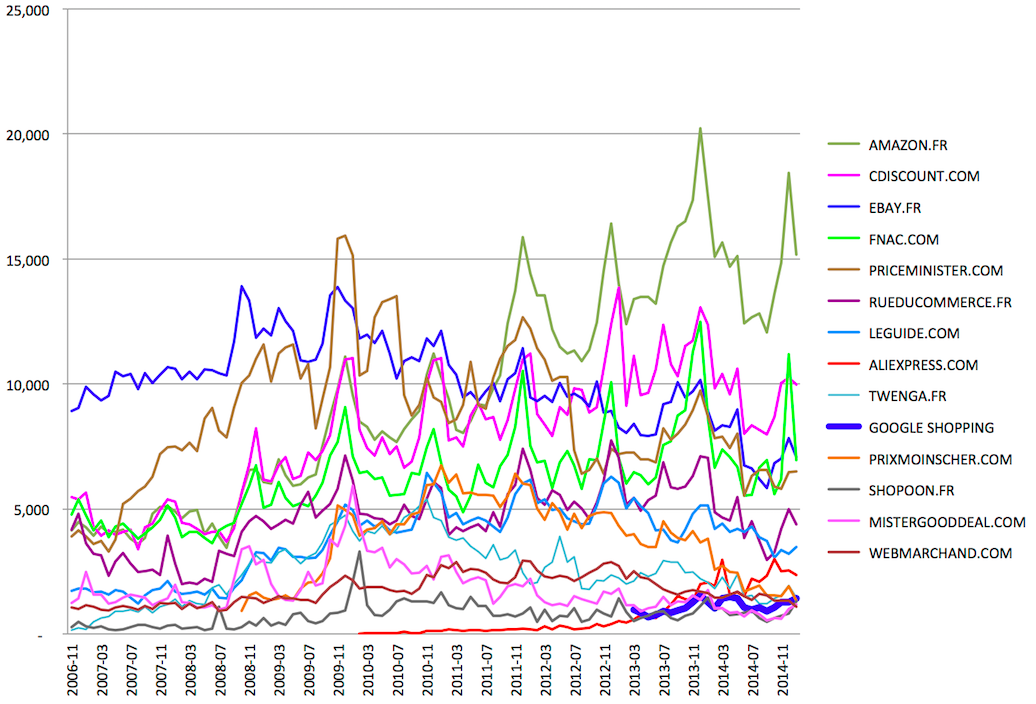
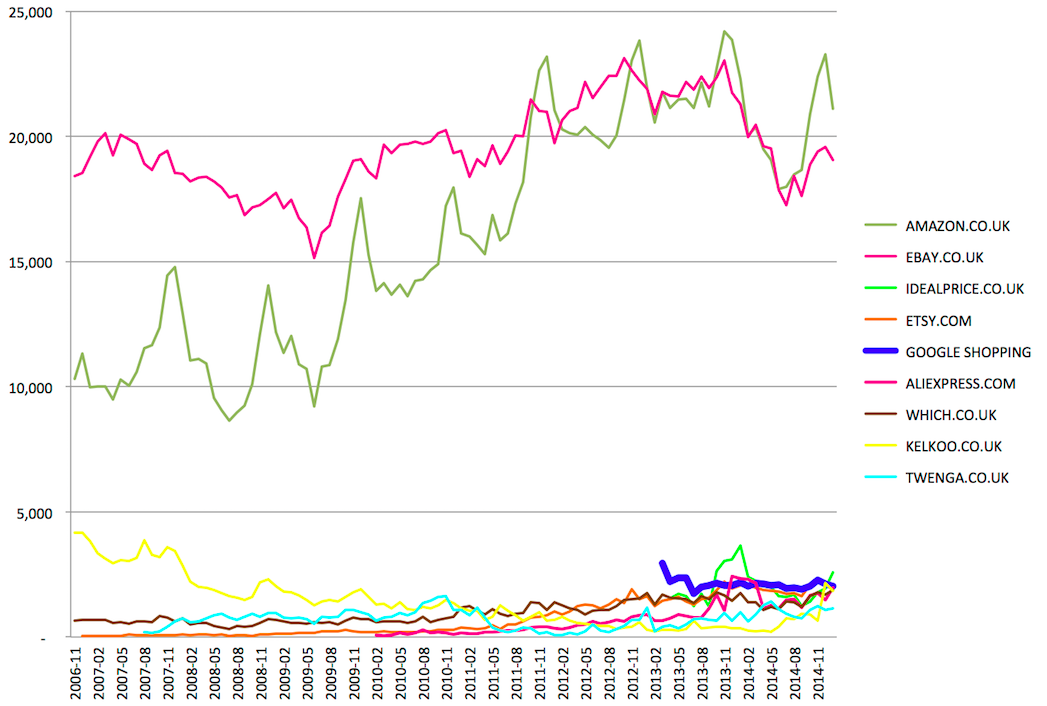
Google also cites online shopping services as a form of competition. The point has merit — many now use Amazon as a product search engine in place of Google for searches that they might have sent before.
[related articles]
However, the strength of that argument is at least tempered in part because Google retain tectonic market share in extant search markets where it could exert undue influence. Merely indicating that mobile matters, and that some search categories are siloed inside of the products of other competitors doesn’t lessen the fact that Google has the capability to act in an anticompetitve manner in other areas.
Certainly that is a less charitable explanation, but it’s worth wearing a mantle of neutraliy until we read the EU’s notes.
Google is correct to point out that its products are no longer such the primal portal for all searches. This becomes even more true as Bing worms its way into the platforms other corporations and as the micro silos of apps subsume the mobile web. But there are points on the scale that still carry weight — and it’s likely that they’ll need to make convincing arguments there in order to parry the objections.
The memo:
Googlers —
As the Financial Times has just reported, the European Commission will tomorrow issue a Statement of Objections (SO) regarding the display and ranking of certain search results, in particular shopping. This is obviously very disappointing news, especially for the search team that has worked so hard to create a great experience for our users over the last 16 years.
First, a few facts about the SO process. An SO is not a final finding. It’s a document in which the Commission staff sets out its preliminary arguments so that the company in question can respond. Expect some of the criticism to be tough. But remember, it’s also an opportunity for Google to tell our side of the story. The back-and-forth over an SO can take some time (even a year or two), and in a number of cases has resulted in the Commission modifying their claims or settling the case. If the two sides cannot settle their differences, the Commission issues an infringement decision, which can be appealed in court.
We have a very strong case, with especially good arguments when it comes to better services for users and increased competition:
Shopping Sites in Germany (unique visitors, ‘000s)
Shopping Sites in France (unique visitors, ‘000s)
Shopping Sites in the UK (unique visitors, ‘000s)
It is the same story with travel–another very competitive vertical:
Travel sites in Germany
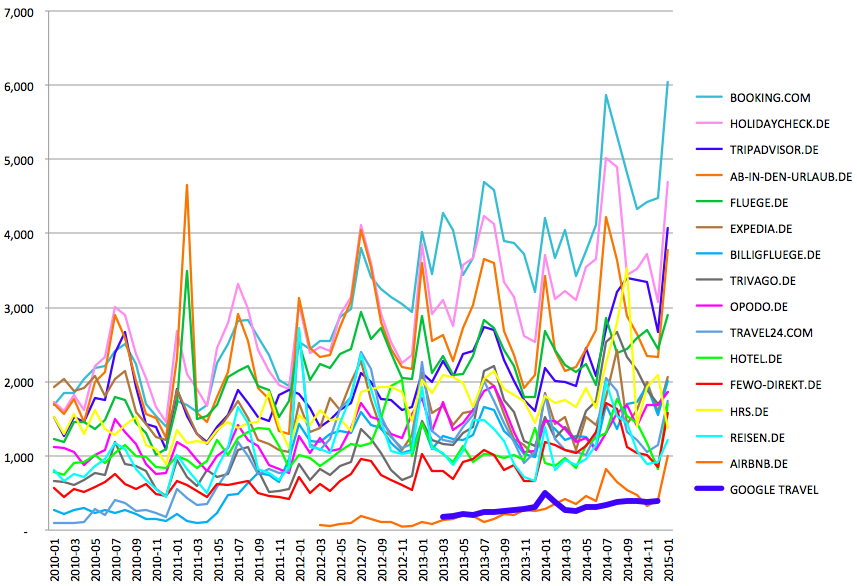
Source: ComScore MMX and Google data (for Google), desktop traffic, unique visitors (‘000s)
We believe that the Commission will also open a formal investigation into Androidtomorrow. This is just the start of a process and does not mean the EC will necessarily take action (for example they opened and closed an inquiry into iTunes a few years ago). We have a very strong case on Android as well:
All told, consumers have a lot of choice — and they are exercising it. And many, many other companies have very successful mobile businesses — including Apple, the most valuable (mobile) company in the world.
Finally, we know the upcoming announcements will be distracting. But you can help in two ways. First, by not commenting on pending legal issues, internally or externally. And second, by focusing on what you all do best … building great products that serve our users and customers.source:http://techcrunch.com/2015/04/14/internal-google-memo-responds-to-eu-antitrust-objections/

